Cover Your SaaS Webinar March 2026
Your SaaS is down. Can You Restore the Business, Not Just the Files?
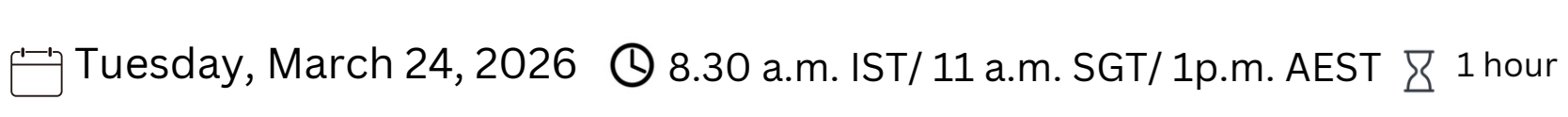
Join Veeam and Reversec Live on March 24 to bridge the gap between “stored data” and “true resilience.”
The 60-Minute Live Session:
- The “Native” Trap: Why legacy assumptions fail in the cloud.
- The Pressure Test: Real-world strategies for approvals and verification.
- Resilience Blueprint: An operating model that actually works under fire.
Featured Speakers:
Daisy Radford | Managing Director, APAC, Reversec
Keith Sng | Field CTO, APJ, Veeam
Please fill out the form below to register for the Webinar