5 Warehouse Fixes That Pay for Themselves
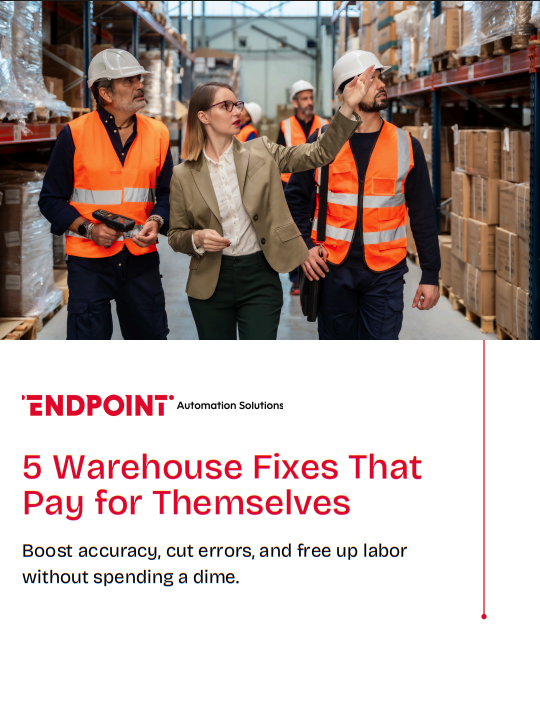
Five warehouse improvements. Five weeks. Under $300. No software
needed.
While you’re evaluating WMS options (or waiting on budget), these five
fixes will tighten accuracy, cut picking time, and eliminate the daily
workarounds your team has learned to live with. Each one comes with
step-by-step implementation, before/after metrics, cost breakdowns, and
common pitfalls.
You’ll walk away with a standardized bin system, color-coded zones,
dedicated staging lanes, a perpetual cycle count process, and a visual
pick priority board.
Please fill out the form below to access the content: