
Mastering Hybrid Cloud Backup Costs, Security and Management
Unlock cost-effective hybrid cloud backup strategies. Learn to secure data and improve efficiency with expert tips in this e-book.
Register to download

Mastering Hybrid Cloud Backup Costs, Security and Management
Unlock cost-effective hybrid cloud backup strategies. Learn to secure data and improve efficiency with expert tips in this e-book.
Register to download

Your Guide to Data Resilience and SIEM Solutions
In a world where threats move fast, integrating your Security Information and Event Management (SIEM) system with your data protection platform can give you a critical edge. This e-book explores how combining Veeam with leading SIEM solutions can strengthen your security posture, streamline operations, and improve response times when it matters most.
Register to download

AI and ML in Backup & Recovery
To gain insight into these AI and ML trends, TechTarget’s Enterprise Strategy Group surveyed 375 IT and data professionals familiar with and/or responsible for data protection (including backup and recovery) decisions and data science for their organization.
Read this exclusive ESG and Veeam eBook to find out more on:
Register to download

Mastering Hybrid Cloud Backup Costs, Security and Management
Unlock cost-effective hybrid cloud backup strategies. Learn to secure data and improve efficiency with expert tips in this e-book.
Register to download

Demystifying Regulatory Compliance: Standards, Frameworks, and Recommendations
The development of regulatory frameworks and standards has emerged from the need to address the challenges and requirements in managing information technology and safeguarding data. These frameworks and standards have not only evolved over time, but they have been shaped by technological advancements and emerging cybersecurity threats.
Register to download

Are You AI Ready?
AI agents are transforming business. Discover how leaders can balance innovation and control through identity, governance, and a clear 90-day roadmap.

Please fill out the form below to access the content:
Related Resources

2025 Gartner Magic Quadrant
For the ninth year in a row, Ping Identity has been named a Leader. Read the report to learn why.

2025 KuppingerCole Leadership Compass: Access Management
Discover why Ping Identity was named a Leader in KuppingerCole’s 2025 Access Management report, with top marks for orchestration, security. and flexibility

2025 Gartner Critical Capabilities
Ping Identity ranks #1 in 3 of 5 use cases in the 2025 Gartner® Critical Capabilities for Access Management. Read the report to learn why.

The Battle for Balance: Minimizing Friction Without Sacrificing Security
Modern IAM eliminates friction and boosts security with adaptive, seamless access – reducing IT overhead, user frustration, and compliance risk.

Please fill out the form below to access the content:
Related Resources

2025 Gartner Magic Quadrant
For the ninth year in a row, Ping Identity has been named a Leader. Read the report to learn why.

2025 KuppingerCole Leadership Compass: Access Management
Discover why Ping Identity was named a Leader in KuppingerCole’s 2025 Access Management report, with top marks for orchestration, security. and flexibility

2025 Gartner Critical Capabilities
Ping Identity ranks #1 in 3 of 5 use cases in the 2025 Gartner® Critical Capabilities for Access Management. Read the report to learn why.

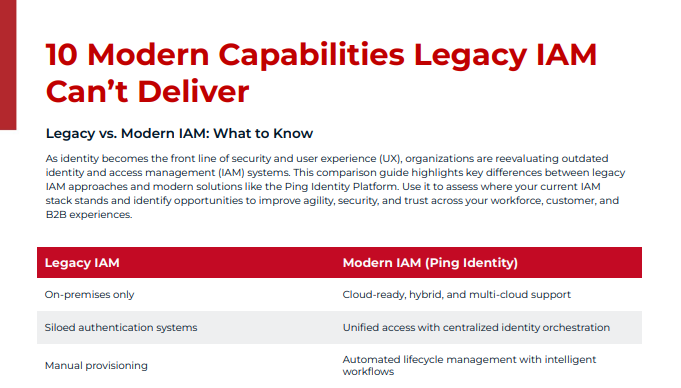
10 Modern Capabilities Legacy IAM Can’t Deliver
Discover 10 critical capabilities legacy IAM lacks – and why modern identity solutions are key to secure, agile, and user-friendly access.
Please fill out the form below to access the content:
Related Resources

2025 Gartner Magic Quadrant
For the ninth year in a row, Ping Identity has been named a Leader. Read the report to learn why.

2025 KuppingerCole Leadership Compass: Access Management
Discover why Ping Identity was named a Leader in KuppingerCole’s 2025 Access Management report, with top marks for orchestration, security. and flexibility

2025 Gartner Critical Capabilities
Ping Identity ranks #1 in 3 of 5 use cases in the 2025 Gartner® Critical Capabilities for Access Management. Read the report to learn why.

Modern Identity: Serious Verification, Seriously Valuable
Your IAM shouldn’t just protect your business – it should grow it
Get our summary to build a business case your CISO and CIO will love:
Please fill out the form below to access the content:
Related Resources

2025 Gartner Magic Quadrant
For the ninth year in a row, Ping Identity has been named a Leader. Read the report to learn why.

2025 KuppingerCole Leadership Compass: Access Management
Discover why Ping Identity was named a Leader in KuppingerCole’s 2025 Access Management report, with top marks for orchestration, security. and flexibility

2025 Gartner Critical Capabilities
Ping Identity ranks #1 in 3 of 5 use cases in the 2025 Gartner® Critical Capabilities for Access Management. Read the report to learn why.

The Future of Identity Is Now – Is Your IAM Ready?
Legacy systems are holding you back. See how IT leaders are unlocking growth, speed and trust
This executive summary lays out why modern identity is a strategic business enabler, not just a security mandate. Here’s a taste of what’s inside:
Please fill out the form below to access the content:
Related Resources

2025 Gartner Magic Quadrant
For the ninth year in a row, Ping Identity has been named a Leader. Read the report to learn why.

2025 KuppingerCole Leadership Compass: Access Management
Discover why Ping Identity was named a Leader in KuppingerCole’s 2025 Access Management report, with top marks for orchestration, security. and flexibility

2025 Gartner Critical Capabilities
Ping Identity ranks #1 in 3 of 5 use cases in the 2025 Gartner® Critical Capabilities for Access Management. Read the report to learn why.