The Radical ROI of Gen AI
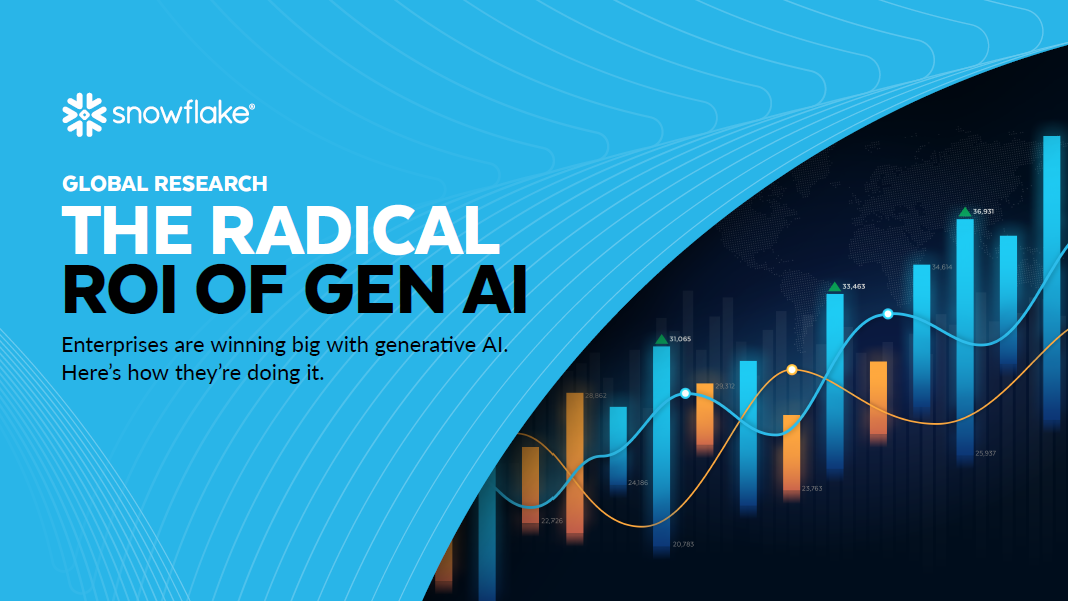
Global research shows that enterprises are winning big with generative AI. We dove into their strategies and measured their outcomes.
Based on research by Enterprise Strategy Group:
- Nearly three in five organizations worldwide are already using gen AI
- 92% of early adopters say their gen AI initiatives have paid for themselves
- Those who have calculated the ROI are seeing a return of 41%
See How Generative AI Has Changed the Game
Researchers at Enterprise Strategy Group surveyed 1,900 business and IT leaders to find out how the first wave of gen AI adoption is changing business.
Short answer: It’s making them richer.
For more, download the full report today.
Please fill out the form below to access the content: